In today’s digital economy, large organizations operate in an environment where cyber threats are not occasional risks but constant realities. Enterprise cybersecurity software has become a critical layer of defense for corporations that manage sensitive customer data, intellectual property, financial systems, and global operations. As cyberattacks grow more sophisticated and costly, enterprises can no longer rely on basic security tools. They require comprehensive cybersecurity solutions designed specifically for large scale infrastructure, complex networks, and regulatory compliance.Example (National Institute of Standards and Technology cybersecurity framework),(Cybersecurity and Infrastructure Security Agency)and (IBM Security enterprise insights) etc.
Enterprise cybersecurity software protects organizations by combining advanced threat detection, real time monitoring, automated response, and centralized control. These platforms are built to secure thousands of endpoints, cloud environments, data centers, and remote users simultaneously. Without enterprise grade protection, even a single vulnerability can lead to data breaches, financial losses, reputational damage, and legal consequences.

The Growing Cybersecurity Challenges Faced by Large Enterprises
Large companies are prime targets for cybercriminals because they store valuable data and operate mission critical systems. Attackers use ransomware, phishing, supply chain attacks, zero day vulnerabilities, and insider threats to exploit weaknesses across enterprise networks. The scale of enterprise operations makes security more complex, especially when organizations rely on hybrid cloud environments, third party vendors, and remote workforces.
Enterprise cybersecurity software addresses these challenges by offering visibility across the entire digital ecosystem. Instead of managing security in isolated tools, enterprises gain a unified platform that monitors networks, endpoints, applications, and data flows. This centralized approach enables faster threat identification and coordinated response across departments.
Advanced Threat Detection and Prevention
One of the most important functions of enterprise cybersecurity software is advanced threat detection. Traditional security tools rely on signature based detection, which is no longer sufficient against modern attacks. Enterprise solutions use artificial intelligence, machine learning, and behavioral analytics to identify suspicious activity before damage occurs.
By analyzing patterns in network traffic, user behavior, and system activity, cybersecurity platforms can detect anomalies that indicate potential breaches. This proactive approach allows security teams to stop threats such as ransomware, advanced persistent threats, and credential theft in real time. High value keywords such as advanced threat protection, endpoint detection and response, and network security solutions reflect the core capabilities that enterprises prioritize when selecting cybersecurity software.
Endpoint Security Across Large Organizations
Large companies manage thousands of devices including laptops, servers, mobile devices, and industrial systems. Each endpoint represents a potential entry point for attackers. Enterprise cybersecurity software provides centralized endpoint protection that ensures consistent security policies across all devices.
Endpoint protection platforms monitor device activity, block malicious files, isolate infected systems, and prevent unauthorized access. With remote work becoming standard, endpoint security has become even more critical. Enterprise solutions ensure that employees working from different locations remain protected without compromising productivity or data integrity.
Many organizations and individuals rely on digital calculators to make smarter financial and strategic decisions before committing resources. Some people calculate investment returns to evaluate long term growth, while others use loan or mortgage calculators to understand monthly payments, interest costs, and repayment timelines. In the same way, businesses often depend on online tools to estimate budgets, forecast expenses, and assess potential risks before moving forward. Providing easy access to calculators on your website helps users plan more accurately, compare options with confidence, and make informed decisions based on clear numerical insights rather than assumptions.
Network Security and Zero Trust Architecture
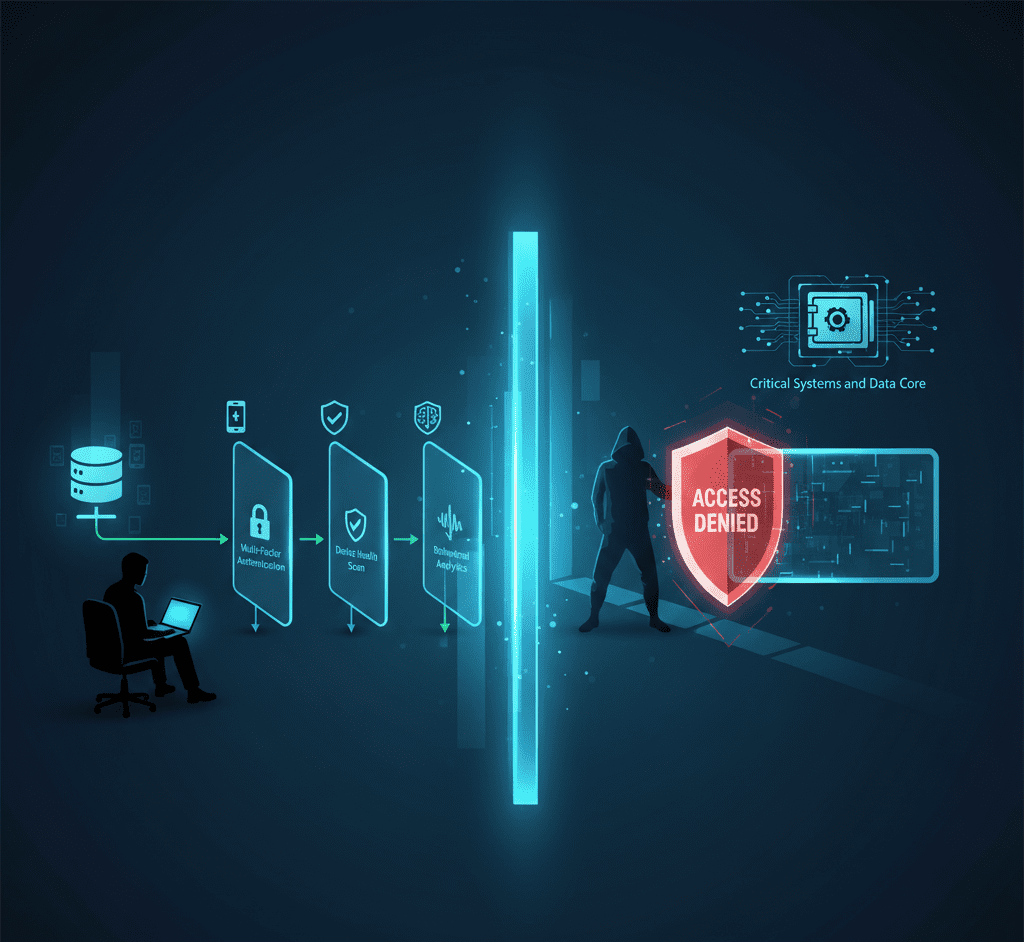
Enterprise cybersecurity software plays a central role in securing internal and external networks. Modern enterprises adopt zero trust security models, which assume that no user or device should be trusted by default. Every access request is verified based on identity, device health, location, and behavior.
Network security tools within enterprise platforms enforce segmentation, monitor traffic, and prevent lateral movement inside the network. This means that even if an attacker gains access to one system, they cannot easily move across the organization. Keywords such as zero trust security, network access control, and enterprise firewall solutions align with high CPM cybersecurity searches and represent essential protections for large companies.
Cloud Security and Hybrid Infrastructure Protection
As enterprises migrate to cloud platforms, protecting cloud workloads becomes a top priority. Enterprise cybersecurity software provides cloud security posture management, workload protection, and identity controls across public, private, and hybrid cloud environments.
These tools continuously assess cloud configurations to identify misconfigurations that could expose sensitive data. They also protect cloud applications from attacks such as data leakage, unauthorized access, and malicious code execution. For enterprises operating across multiple cloud providers, centralized cloud security ensures consistent enforcement and compliance.
Data Protection and Information Security
Data is one of the most valuable assets for large organizations. Enterprise cybersecurity software protects sensitive information through encryption, data loss prevention, and access control. These tools ensure that confidential data remains secure whether it is stored, processed, or transmitted.
Data protection features monitor how information is accessed and shared across the organization. If sensitive data is moved outside approved channels or accessed without authorization, the system can block the action or alert security teams. This level of control is essential for industries such as finance, healthcare, and technology where data breaches can result in severe penalties.
Identity and Access Management
Identity based attacks are among the most common threats faced by enterprises. Enterprise cybersecurity software includes identity and access management solutions that control who can access systems and data. These platforms enforce multi factor authentication, role based access, and continuous verification.
By integrating identity security with other cybersecurity components, enterprises reduce the risk of compromised credentials leading to full system access. Identity security ensures that users only access the resources they need, limiting the impact of insider threats and stolen credentials.
Automated Incident Response and Security Operations
Speed is critical when responding to cyber incidents. Enterprise cybersecurity software automates incident detection, analysis, and response. When a threat is detected, the system can automatically isolate affected systems, block malicious traffic, and initiate remediation processes.
Security orchestration and automated response reduce the burden on security teams and minimize response times. For large enterprises managing global operations, automation ensures consistent handling of security incidents across regions and time zones.
Compliance and Regulatory Protection
Large companies must comply with various cybersecurity regulations and data protection laws. Enterprise cybersecurity software supports compliance by enforcing security policies, maintaining audit logs, and generating compliance reports.
Regulatory frameworks such as data protection standards and industry specific requirements demand continuous monitoring and documentation. Enterprise platforms simplify compliance management by aligning security controls with regulatory obligations. This reduces legal risk and demonstrates due diligence to regulators and stakeholders.
Centralized Visibility and Risk Management
One of the strongest advantages of enterprise cybersecurity software is centralized visibility. Security leaders gain a comprehensive view of risks, vulnerabilities, and threats across the organization. Dashboards provide real time insights into security posture, enabling informed decision making.
Risk management tools help enterprises prioritize vulnerabilities based on potential impact. Instead of reacting to every alert, organizations focus resources on the most critical risks. This strategic approach improves overall security effectiveness and aligns cybersecurity investments with business objectives.

The Business Value of Enterprise Cybersecurity Software
Beyond protection, enterprise cybersecurity software delivers measurable business value. It reduces downtime caused by cyber incidents, protects brand reputation, and safeguards customer trust. Strong cybersecurity also enables digital transformation by allowing enterprises to adopt cloud services and remote work securely.
Investing in enterprise grade cybersecurity software is not just a technical decision but a strategic one. Companies with robust security frameworks are better positioned to grow, innovate, and compete in a digital marketplace where trust and resilience are essential.
Conclusion
Enterprise cybersecurity software protects large companies by providing advanced threat detection, endpoint security, network protection, cloud security, data protection, and automated response capabilities. These platforms address the unique challenges of large scale operations and evolving cyber threats. As attacks become more complex and regulations more demanding, enterprise cybersecurity software remains a foundational pillar of modern business security.